wp-k8s: WordPress on Kubernetes project (GKE, cloud SQL, NFS, cluster autoscaling, HPA, VPA, Ingress, Let's Encrypt) - FoolControl: Phear the penguin

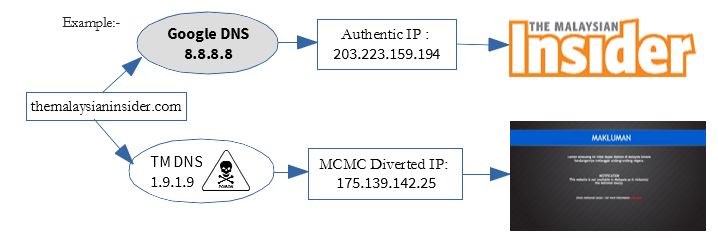
Malaysia election: Politicians claim phones hacked; probe shows spam calls from unknown bot attacks | The Straits Times

The Gas Siphon Attack: The Technical and Economic Realities Behind Hacking Exchanges · Devcon Archive: Ethereum Developer Conference

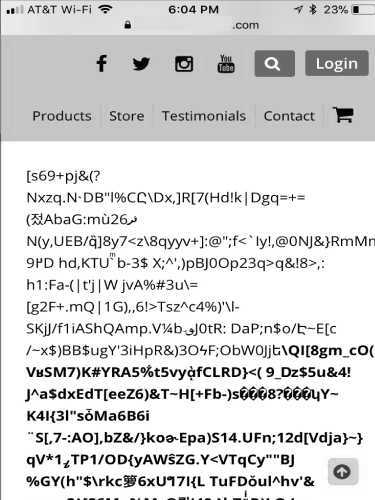
Sensors | Free Full-Text | Code Injection Attacks in Wireless-Based Internet of Things (IoT): A Comprehensive Review and Practical Implementations
Combating Information Manipulation: A Playbook for Elections and Beyond | International Republican Institute
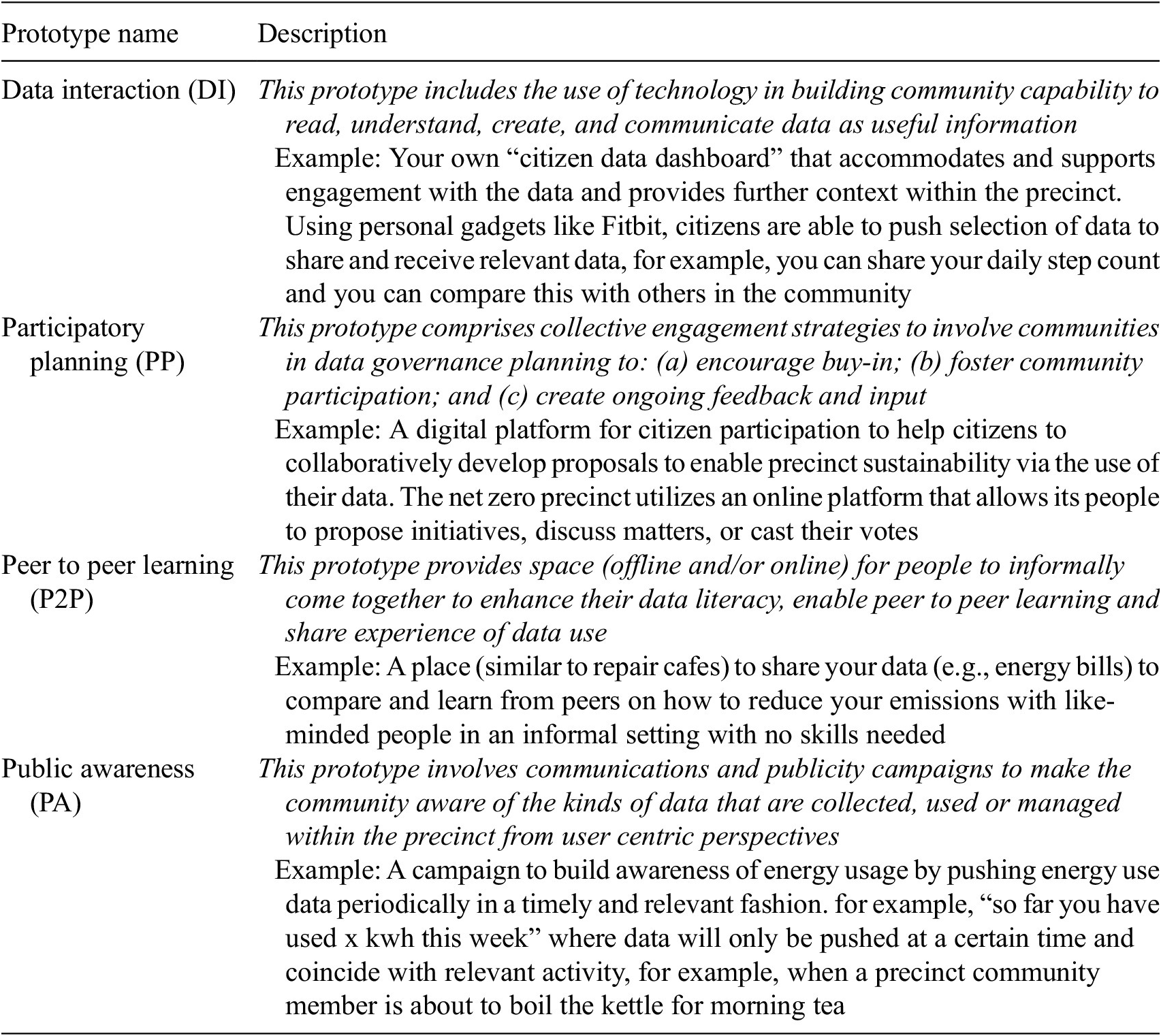
A participatory approach for empowering community engagement in data governance: The Monash Net Zero Precinct | Data & Policy | Cambridge Core



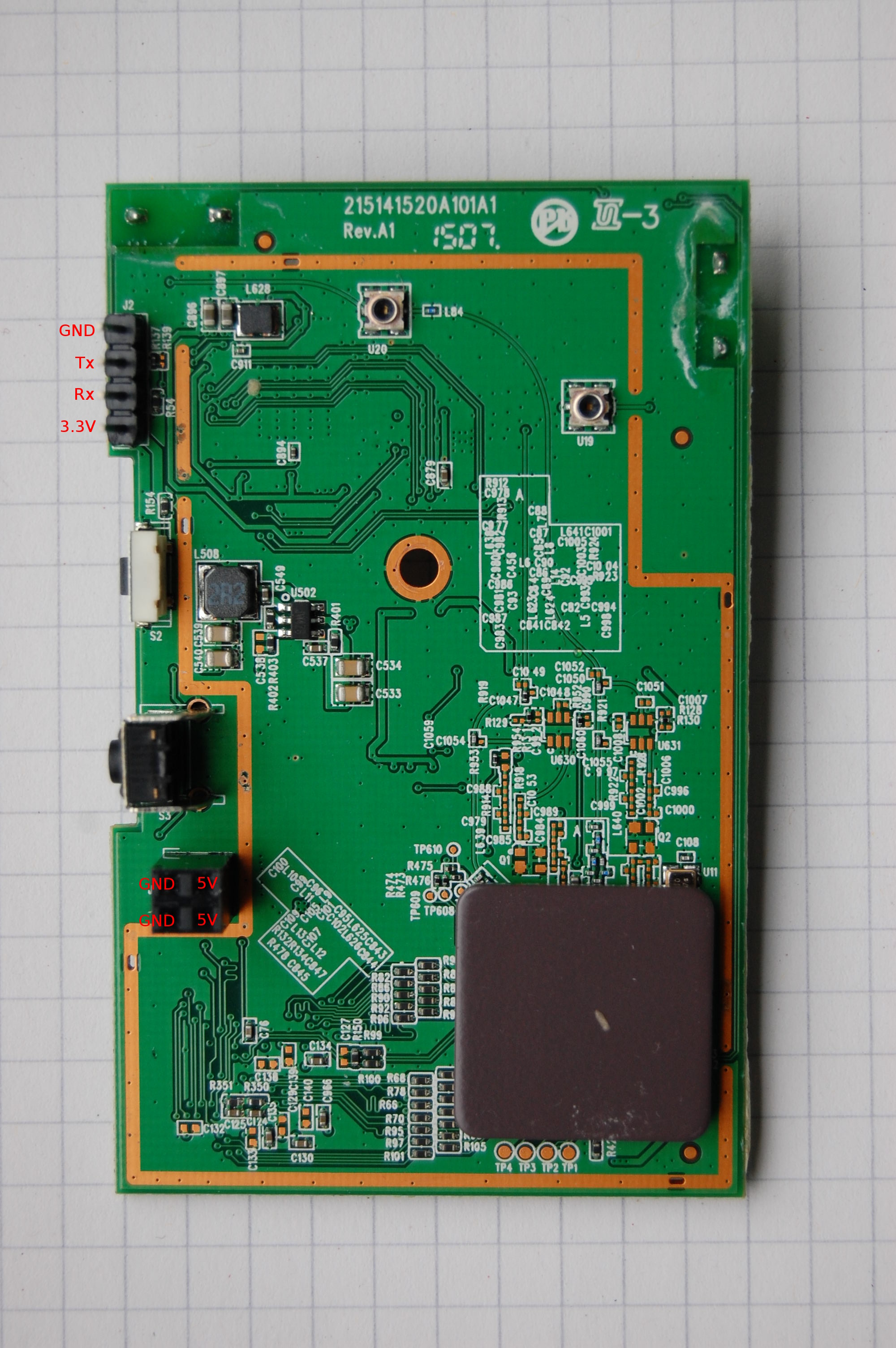
![Exploitation] D-Link DAP-1860 Vulnerability | by Infiniti Team | Medium Exploitation] D-Link DAP-1860 Vulnerability | by Infiniti Team | Medium](https://miro.medium.com/v2/resize:fit:1400/0*6Cs6yeRlMB6wIozc.png)
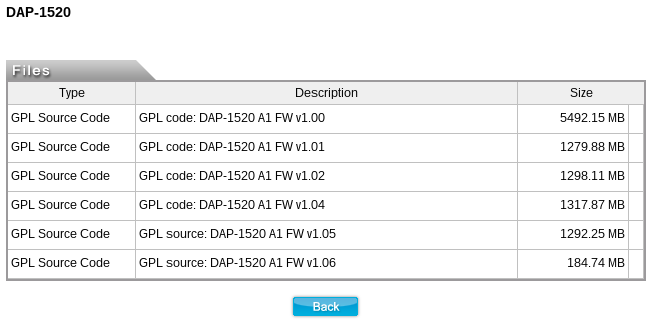

![Exploitation] D-Link DAP-1860 Vulnerability | by Infiniti Team | Medium Exploitation] D-Link DAP-1860 Vulnerability | by Infiniti Team | Medium](https://miro.medium.com/v2/resize:fit:988/0*R4W3w1UlpAdzrNbA.png)